Ipsec/l2tp For Mac
Contents. History Published in 1999 as proposed standard, L2TP has its origins primarily in two older tunneling protocols for point-to-point communication: 's (L2F) and 's (PPTP). A new version of this protocol, appeared as proposed standard in 2005. L2TPv3 provides additional security features, improved encapsulation, and the ability to carry data links other than simply (PPP) over an (for example:, etc.).
Description The entire L2TP packet, including and L2TP, is sent within a (UDP). A virtue of transmission over UDP (rather than TCP; c.f. ) is that it avoids the 'TCP meltdown problem'. It is common to carry sessions within an L2TP tunnel.
L2TP does not provide confidentiality or strong authentication by itself. Is often used to secure L2TP packets by providing confidentiality, authentication and integrity. The combination of these two protocols is generally known as L2TP/IPsec (discussed below). The two endpoints of an L2TP tunnel are called the LAC ( L2TP Access Concentrator) and the LNS ( L2TP Network Server). The LNS waits for new tunnels.
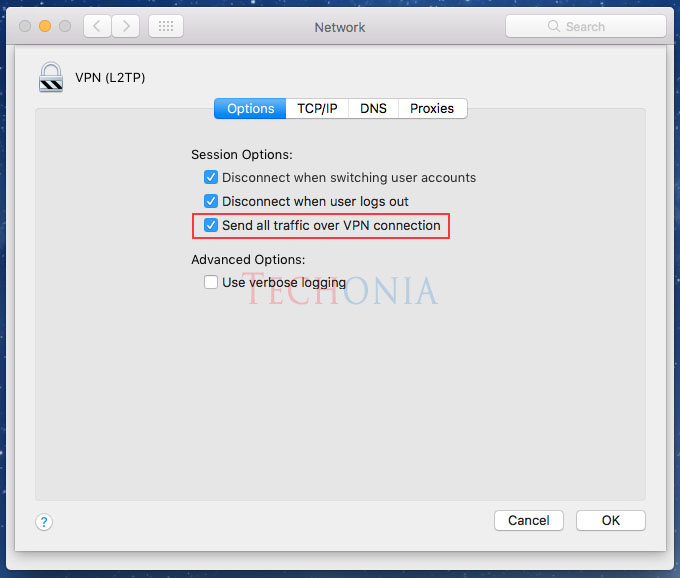
Oct 26, 2018 - Manually set up a VPN connection on Mac OS X using L2TP with this. Note: L2TP-IPsec provides weak security benefits and should only be.
Once a tunnel is established, the network traffic between the peers is bidirectional. To be useful for networking, higher-level protocols are then run through the L2TP tunnel. To facilitate this, an L2TP session (or ' call') is established within the tunnel for each higher-level protocol such as PPP. Either the LAC or LNS may initiate sessions. The traffic for each session is isolated by L2TP, so it is possible to set up multiple virtual networks across a single tunnel.
Should be considered when implementing L2TP. The exchanged within an L2TP tunnel are categorized as either control packets or data packets. L2TP provides reliability features for the control packets, but no reliability for data packets. Reliability, if desired, must be provided by the nested protocols running within each session of the L2TP tunnel.
L2tp Ipsec Port
L2TP allows the creation of a virtual private dialup network (VPDN) to connect a remote client to its corporate network by using a shared infrastructure, which could be the Internet or a service provider's network. Tunneling models An L2TP tunnel can extend across an entire PPP session or only across one segment of a two-segment session. This can be represented by four different tunneling models, namely:. voluntary tunnel.
compulsory tunnel — incoming call. compulsory tunnel — remote dial. L2TP connection L2TP packet structure An L2TP packet consists of: Bits 0–15 Bits 16–31 Flags and Version Info Length (opt) Tunnel ID Session ID Ns (opt) Nr (opt) Offset Size (opt) Offset Pad (opt). Payload data Field meanings: Flags and version control flags indicating data/control packet and presence of length, sequence, and offset fields. Length (optional) Total length of the message in bytes, present only when length flag is set. Tunnel ID Indicates the identifier for the control connection. Session ID Indicates the identifier for a session within a tunnel.
Ns (optional) sequence number for this data or control message, beginning at zero and incrementing by one (modulo 2 16) for each message sent. Present only when sequence flag set. Nr (optional) sequence number for expected message to be received.
Nr is set to the Ns of the last in-order message received plus one (modulo 2 16). In data messages, Nr is reserved and, if present (as indicated by the S bit), MUST be ignored upon receipt. Offset Size (optional) Specifies where payload data is located past the L2TP header.
If the offset field is present, the L2TP header ends after the last byte of the offset padding. This field exists if the offset flag is set. Offset Pad (optional) Variable length, as specified by the offset size. Contents of this field are undefined. Payload data Variable length (Max payload size = Max size of UDP packet − size of L2TP header) L2TP packet exchange At the time of setup of L2TP connection, many control packets are exchanged between server and client to establish tunnel and session for each direction. One peer requests the other peer to assign a specific tunnel and session id through these control packets.
Then using this tunnel and session id, data packets are exchanged with the compressed PPP frames as payload. The list of L2TP Control messages exchanged between LAC and LNS, for handshaking before establishing a tunnel and session in voluntary tunneling method are L2TP/IPsec Because of the lack of confidentiality inherent in the L2TP protocol, it is often implemented along with. This is referred to as L2TP/IPsec, and is standardized in. The process of setting up an L2TP/IPsec VPN is as follows:.
Negotiation of IPsec (SA), typically through (IKE). This is carried out over UDP port 500, and commonly uses either a shared password (so-called '), public keys, or certificates on both ends, although other keying methods exist. Establishment of (ESP) communication in transport mode.
The IP protocol number for ESP is 50 (compare TCP's 6 and UDP's 17). At this point, a secure channel has been established, but no tunneling is taking place. Negotiation and establishment of L2TP tunnel between the SA endpoints. The actual negotiation of parameters takes place over the SA's secure channel, within the IPsec encryption. L2TP uses UDP port 1701.
When the process is complete, L2TP packets between the endpoints are encapsulated by IPsec. Since the L2TP packet itself is wrapped and hidden within the IPsec packet, the original source and destination IP address is encrypted within the packet.
Also, it is not necessary to open UDP port 1701 on firewalls between the endpoints, since the inner packets are not acted upon until after IPsec data has been decrypted and stripped, which only takes place at the endpoints. A potential point of confusion in L2TP/IPsec is the use of the terms tunnel and secure channel.
The term tunnel-mode refers to a channel which allows untouched packets of one network to be transported over another network. In the case of L2TP/PPP, it allows L2TP/PPP packets to be transported over IP. A secure channel refers to a connection within which the confidentiality of all data is guaranteed. In L2TP/IPsec, first IPsec provides a secure channel, then L2TP provides a tunnel. Windows implementation provides two new configuration utilities that attempt to make using L2TP without IPsec easier, both described in sections that follow below:.

an called 'Windows Firewall with Advanced Security' (WFwAS), located in Control Panel → Administrative Tools. the ' advfirewall' command-line tool Both these configuration utilities are not without their difficulties, and unfortunately, there is very little documentation about both 'netsh advfirewall' and the IPsec client in WFwAS. One of the aforementioned difficulties is that it is not compatible with. Another problem is that servers must be specified only by IP address in the new Vista configuration utilities; the hostname of the server cannot be used, so if the IP address of the IPsec server changes, all clients will have to be informed of this new IP address (which also rules out servers that addressed by utilities such as ). L2TP in ISPs' networks L2TP is often used by ISPs when internet service over for example or cable is being resold. From the end user, packets travel over a wholesale network service provider's network to a server called a Broadband Remote Access Server , a protocol converter and router combined.
On legacy networks the path from end user customer premises' equipment to the BRAS may be over an network. From there on, over an IP network, an L2TP tunnel runs from the BRAS (acting as LAC) to an LNS which is an edge router at the boundary of the ultimate destination ISP's IP network. See also. References. IETF (1999), Layer Two Tunneling Protocol 'L2TP'. Retrieved 2014-07-28. Point-to-Point Tunneling Protocol (PPTP) : A data-link layer protocol for wide area networks (WANs) based on the Point-to-Point Protocol (PPP) and developed by Microsoft that enables network traffic to be encapsulated and routed over an unsecured public network such as the Internet.
Titz, Olaf (2001-04-23). Retrieved 2015-10-17. Honda, Osamu; Ohsaki, Hiroyuki; Imase, Makoto; Ishizuka, Mika; Murayama, Junichi (October 2005). 'Understanding TCP over TCP: effects of TCP tunneling on end-to-end throughput and latency'. Missing or empty url= ; access-date= requires url=. External links Implementations.
Cisco:, also read. Open source and Linux:, (inactive),. Microsoft: built-in client included with Windows 2000 and higher; for Windows 98/Windows Me/Windows NT 4.0. Apple: built-in client included with Mac OS X 10.3 and higher.